Recovering Ransomware-Encrypted Files: Part 1
This is part one of a three part series on what to do if your files have been encrypted by ransomware. You can jump straight to part two or part three, but also be sure to read how to spot a phishing attack.
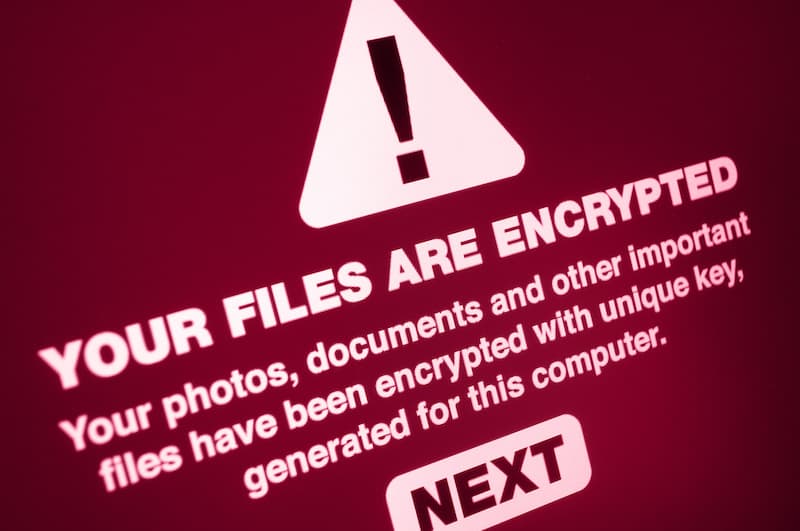
Ransomware is a type of malware that encrypts all of your data so that it can no longer be accessed by you, before demanding payment for the files to be decrypted. If it happens to you, what do you do?

Call the cops? the telecommunications ombudsman? the FBI?
You can (and should) do all of the above, but unfortunately law enforcement is extremely unlikely to be able to help in getting your files back.
1. Recover from a backup
After removing the ransomware from the system and ensuring the hackers cannot again access your system, the first step is to see if there is a valid backup you can restore a backup of files from.
Unfortunately most current ransomware software will search for and delete any backups it finds, but it is still worth checking to see if there is any:
- Shadow copies\previous versions
- Windows System Restore Points
- Copies of important data saved to NextCloud, OneDrive, Google Drive, Dropbox or other cloud file service.
- Backups on external drives or network storage.
- Virtual machine snapshots.
2. Use a Ransomware Decryptor
As a rule of thumb, a file encrypted with ransomware cannot be encrypted. There are however some cases in which law enforcement have caught the hacker responsible for a certain version of ransomware and release the decryption key.
Unfortunately this only applies to a limited pool of ransomware, so if you have been recently infected then this likely wont be of much help, still it is worth a go. If you can afford to wait, new decryption keys become available all the time as cybercriminals are caught, so even though there isn’t a decryption key available today, there may be one in the future. .
Here are a few reputable sites that may have a decryption tool available for you to use to recover your files:
A Google search will return plenty more, however if a site wants you to sign up for a service, or pay money in order to decrypt files then it is likely also a scam site, which leads to…
3. Beware of further scams
Unfortunately scammers gotta scam, and even when you are down they will still take the opportunity to hurt you further… And sometimes even those who are supposed to help you are trying to scam you.
Stay vigilant!
Scottish IT service provider Red Mosquito was found to be running a side business in which they “decrypted” ransomware by contacting the ransomware author and negotiating a price for the scrambled files, then charging the customer an exorbitant amount for the “decryption.”
The scam was uncovered by researchers at Emisoft, who posed as both a ransomware victim and the ransomware author. Red Mosquito contacted the fictitious ransomware author and negotiated the price of decryption down to $900, then contacted the equally fictitious victim and cited a fee of $3950 for the decryption. Barrister Tim Forte, who practices criminal law, confirmed that the behavior is criminal conduct.
This is a good reminder that if you are utilizing the services of a technology company to decrypt files for you, make sure that they are willing to be transparent about the process that they use.
Recent Comments